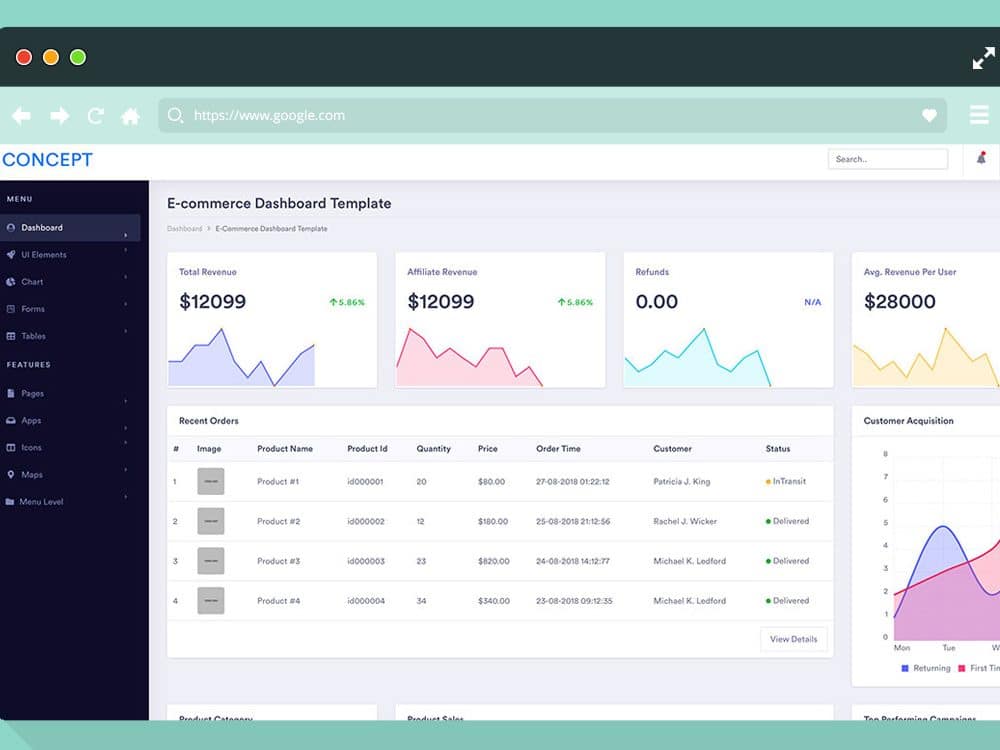
50 Best Admin Dashboard Templates 2026
HTML admin dashboard templates provide a clean foundation for building web applications, content management systems, and analytics dashboards. They come with pre-built UI components, responsive layouts, and organized code that…